
How To Protect My Wi-Fi Network
Your Wi-Fi network is the gateway to your digital life, your devices, your data, and in many cases, your business operations. A weak or unsecured network invites trouble, threat actors intercepting data, IoT devices (doorbell cameras, thermostats) getting hijacked, or even ransomware. If a threat actor gains access to your Wi-Fi, they often don’t need to hack anything else, they are already inside your network perimeter. Many cyber incidents start with compromised wireless networks because they are the least secured entry point in a small business or home office. Below are the most effective ways to secure your Wi-Fi network.
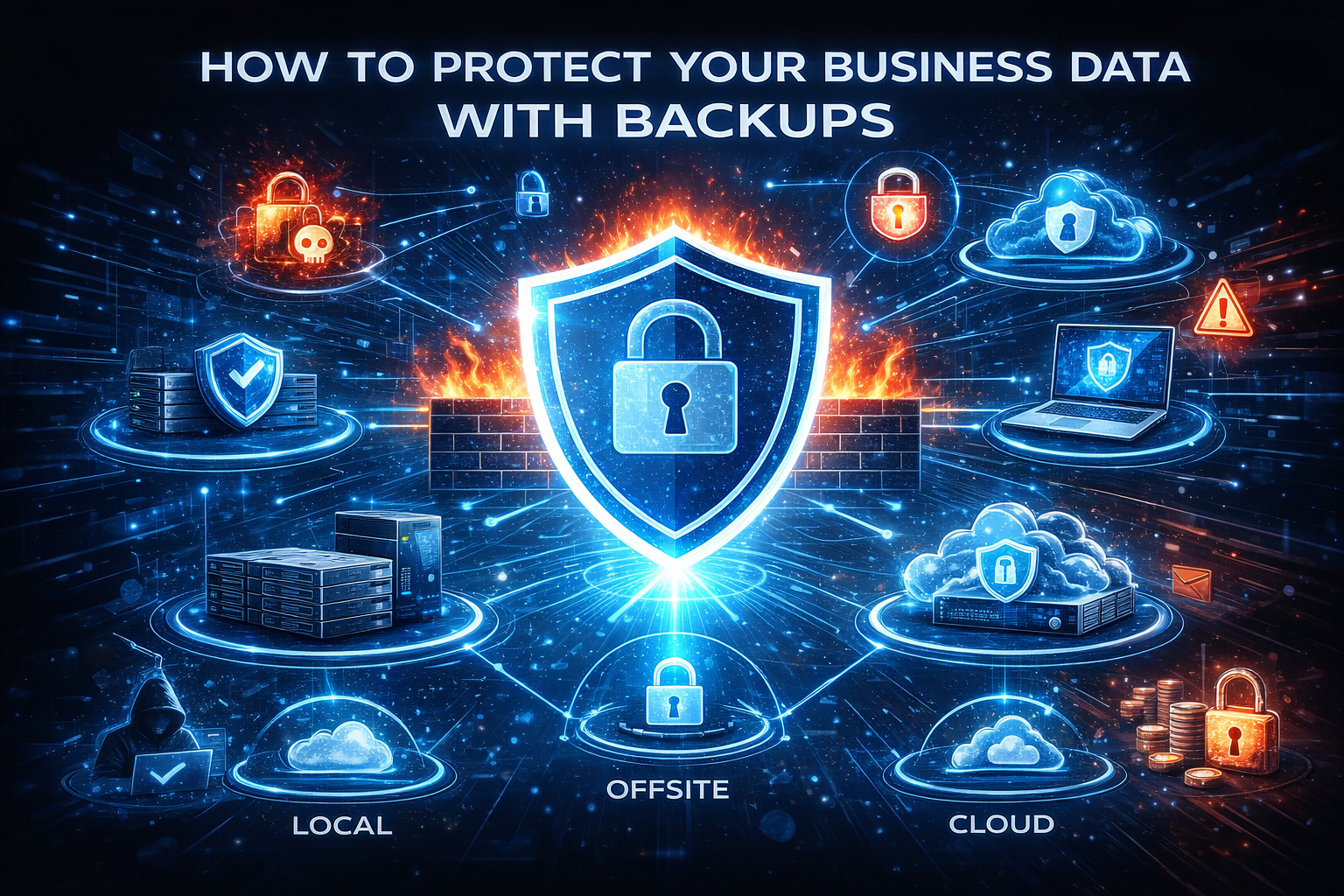
How To Protect Your Data with Backups
For most small to medium sized businesses, data is the business. The accounting system, customer related documents, emails, even passwords live in digital form. Companies rarely go out of business because of a threat actor alone, they go out of business because they lose their data. Yet many businesses underestimate how quickly data can be lost. Hardware failures, cyberattacks, human error, natural disasters, or even simple software glitches can disrupt operations and cause permanent data loss. The companies that recover are the ones with a structured backup and recovery strategy in place before the incident occurred.

Importance of Network Perimeter Security
In an era where cyber threats grow more sophisticated by the day, organizations must take proactive steps to defend their digital environments. Many organizations assume threat actors are inside the network, while insider threats and compromised credentials are real risks. The network perimeter remains a critical line of defense. Network perimeter security is no longer just about blocking traffic. It is about controlling access, inspecting behavior, and reducing exposure before threats ever reach internal systems.

Why Keep Your Software Up to Date
In today’s digital world cyber threats evolve faster than ever. Whether you are managing a business, leading a team, or just trying to protect your personal devices, keeping your software up to date is one of the most effective and affordable ways to stay secure. For many people software updates are viewed as an inconvenience, something that interrupts productivity and can be done later, and threat actors are counting on that mindset. Unpatched software remains one of the most common causes of security breaches. Keeping your software up to date is not the best practice, but a fundamental security requirement.
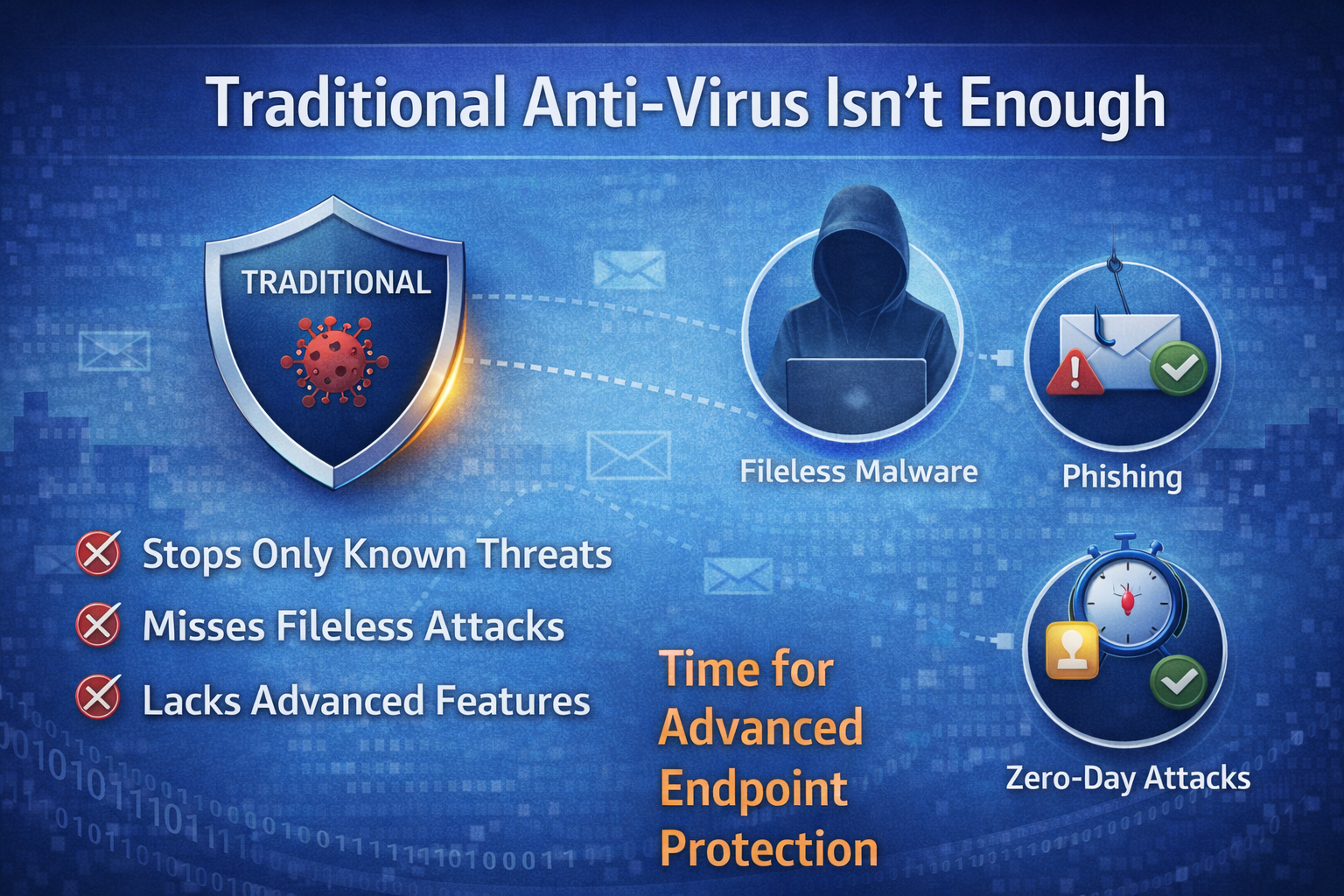
Traditional Anti-Virus Isn't Enough Anymore
In today’s threat landscape, threat actors are now targeting companies of all sizes. Where cyber threats grow more sophisticated daily, companies face unprecedented challenges in securing their networks, devices, and data. Threat actors now actively target organizations of all sizes, often exploiting endpoints, desktops, laptops, mobile devices, and servers, as entry points to compromise networks. Endpoint Detection and Response (EDR) combined with Zero-Trust security model has emerged as a cornerstone of modern cybersecurity strategies. We understand that traditional security methods are no longer enough. We will explore how EDR and Zero-Trust work together to secure your network and by the end you will know why this combination is critical for safeguarding your network.

Benefits of a Unified Security Platform
In the digital world we live in the cyber threats we face are growing and more advanced than ever before. One of the most effective and often overlooked ways to protect your company is by focusing on identity and access management. If you have read my articles on (Security Starts with Strong Passwords link) and (Cybersecurity Awareness and Phishing Training link) you understand the importance of your passwords and training your employees to be security focused. Identity management forms the backbone of a secure environment, ensuring only authorized users access sensitive systems and data. When you add multi-factor authentication with your identity management it strengthens your security posture.

Identity Management and Multi-Factor Authentication
In the digital world we live in the cyber threats we face are growing and more advanced than ever before. One of the most effective and often overlooked ways to protect your company is by focusing on identity and access management. If you have read my articles on (Security Starts with Strong Passwords link) and (Cybersecurity Awareness and Phishing Training link) you understand the importance of your passwords and training your employees to be security focused. Identity management forms the backbone of a secure environment, ensuring only authorized users access sensitive systems and data. When you add multi-factor authentication with your identity management it strengthens your security posture.

Protecting Your Email Ecosystem: DMARC, SPF, and DKIM
Email remains one of the most widely used communication channels for businesses, the threat of phishing and spoofing looms larger than ever. Email remains the primary attack vector for threat actors. Phishing, spoofing, and business email compromise continue to increase year over year, costing companies financially, operational disruption, and reputational damage. Major providers like Google, Yahoo, and Microsoft now strictly enforce email authentication protocols, rejecting non-compliant messages.
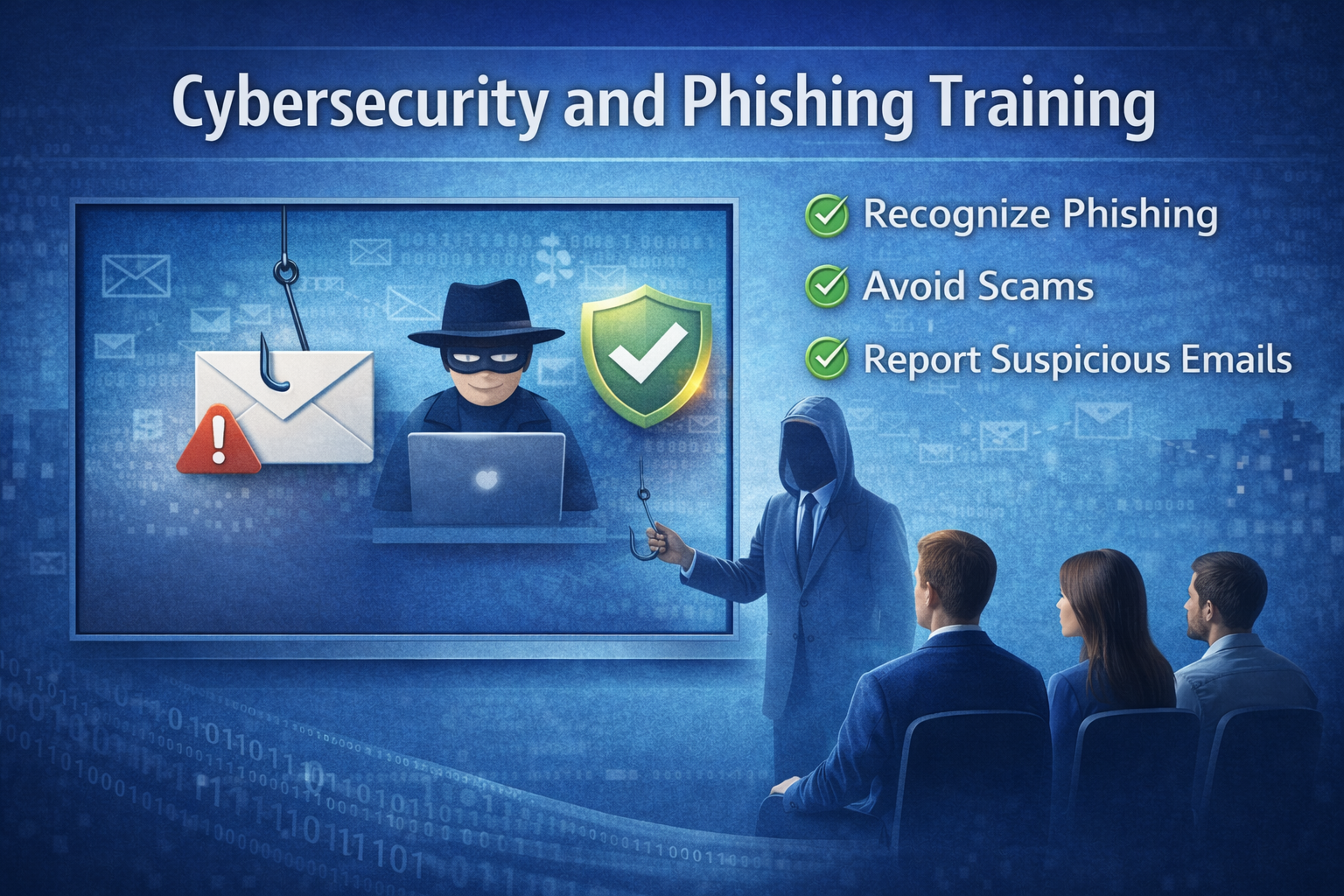
Cybersecurity Awareness and Phishing Training
In today’s digital world, small to medium-sized businesses (SMBs) face an ever-growing array of cyber threats, and one of the most persistent and damaging threats is phishing. The consequences of a single security lapse can be devastating, leading to financial loss, reputation damage, and operational disruptions. Despite the advances in security technology, human error remains one of the top causes of breaches, and phishing emails are the most common method threat actors use to exploit weakness. For SMBs, which often have fewer resources than larger companies, fostering cybersecurity awareness and implementing effective phishing training are essential. If you read the last post, Security Starts with Strong Passwords (link), now you know how to create a strong password. Now I am going to explain why cybersecurity awareness and phishing training is an essential part of any modern security strategy.

Security Starts with Strong Passwords
In today’s digital landscape, passwords are the first line of defense for our personal and professional data. With the ever-growing threat landscape and the advancement of biometric login, multi-factor authentication, and encryption, passwords remain the cornerstone of cybersecurity. Unfortunately, they are also one of the weakest links often due to human error, negligence, or outdated practices. Mastering the art of creating and managing strong passwords is no longer optional, it’s essential. In this article I will try and help you with some of the best practices for creating and managing strong passwords.

