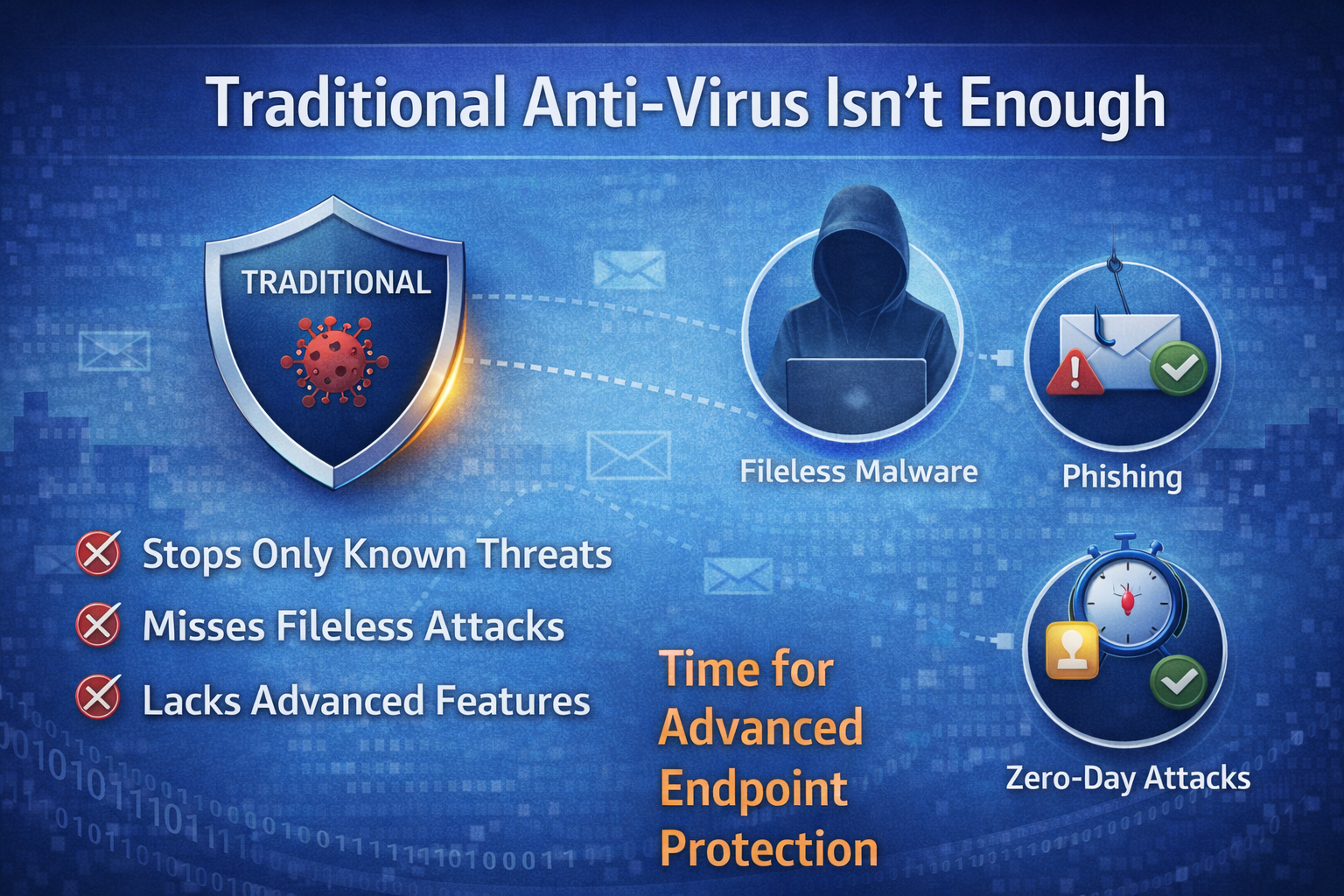
Traditional Anti-Virus Isn't Enough Anymore
In today’s threat landscape, threat actors are now targeting companies of all sizes. Where cyber threats grow more sophisticated daily, companies face unprecedented challenges in securing their networks, devices, and data. Threat actors now actively target organizations of all sizes, often exploiting endpoints, desktops, laptops, mobile devices, and servers, as entry points to compromise networks. Endpoint Detection and Response (EDR) combined with Zero-Trust security model has emerged as a cornerstone of modern cybersecurity strategies. We understand that traditional security methods are no longer enough. We will explore how EDR and Zero-Trust work together to secure your network and by the end you will know why this combination is critical for safeguarding your network.
For decades, antivirus software was the cornerstone of cybersecurity. It scanned files, detected known malware signatures, and kept systems relatively safe. But the threat landscape has changed dramatically, and traditional antivirus can no longer protect your company.
Why Endpoints Are the New Front Line
Endpoints are where users and threat actors meet. Whether it’s a phishing email or a drive-by download from a malicious website, endpoints serve as the initial point of infection. Once compromised, the threat actor can move around the network, infect other endpoints, or steal proprietary data, often without detection.
The Evolution of Cyber Threats
Threat actors today use sophisticated techniques that bypass signature-based detection. Modern attacks include:
- Fileless Malware – This type of attack operated in memory, leaving no traditional file for antivirus to scan.
- Zero-Day Exploit – Takes advantage of software bugs before they are patched, making signature-based tools ineffective.
- Phishing and Social Engineering – Targets users directly. See our article Cybersecurity and Phishing Training.
- Ransomware-as-a-Service – Threat actors rent attack kits, making ransomware more accessible and widespread.
Traditional antivirus was designed for a world where threats were static and predictable. Today the threats are dynamic, automated, and often human-operated.
What is Endpoint Detection and Response (EDR)?
Endpoint Detection and Response is a cybersecurity solution designed to continuously monitor, detect, investigate, and respond to threats on the endpoint. Unlike traditional antivirus software, which focuses mainly on known malware, signature-based detection. EDR take a proactive and comprehensive approach, using behavioral analysis, machine learning, and threat intelligence to identify suspicious activities and respond swiftly.
Key Components of EDR
- Continuous Monitoring – EDR solutions collect and analyze data from endpoints in real time, track processes, file changes, network connections, and user activities.
- Threat Detection – Using behavioral analytics and threat intelligence, EDR identifies anomalies that may indicate the signs of an infection.
- Incident Investigation – EDR provides detailed information, allowing teams to trace the root cause of an infection, understand its scope, and assess its impact.
- Automated Responses – EDR can automatically isolate infected endpoint, block malicious processes, or roll back changes.
- Integration with Security Systems – EDR platforms often integrate with security platforms like a Unified Security Platform (link) for a holistic defense.
EDR is particularly valuable tool to defend against these modern threats everyone faces. However, EDR alone is not the complete solution, it thrives when paired with a security framework like Zero-Trust.
The Zero-Trust Security Model
Zero-Trust is a security philosophy that assumes that no user, device, or network is inherently trustworthy. It is built on the principle of never trust, always verify. Zero-Trust enforces continuous verification of users, devices, and applications, regardless of their location or role. Trust is not permanent, it’s earned and re-evaluated regularly.
Core Principles or Zero-Trust
- Least Privilege Access – Users only get the access they need
- Verify Explicitly – Every user and device must be authenticated and authorized using multiple factors, such as MFA and device health checks.
- Continuous Monitoring – Logs and behavioral analytics to detect anomalies
- Data-Centric Security – Protecting data is prioritized
Zero-Trust shifts security from a perimeter-based model to one that focuses on protecting individual assets, making it ideal for today’s distributed work environments.
Why Combine EDR and Zero-Trust
EDR and Zero-Trust are complementary approaches that address different aspects of cybersecurity. EDR focuses on threats on the endpoint, while zero-trust ensures that only verified entities can access resources. When combined, they create a proactive and adaptive security posture.
1. Prevention and Detection
- Zero-Trust policies help prevent unauthorized access
- EDR detects and responds when something gets past those defenses
2. Device Health Enforcement
- Zero-Trust validates whether an endpoint meets security requirements
- EDR provides the necessary data, patch level, antivirus status, suspicious activity, to enforce compliance
3. Faster Response to Threats
- If EDR detects malicious behavior, it can isolate the device from the network automatically
- Zero-Trust ensures that even if one endpoint is compromised, threat actors can’t freely move across the network.
4. Improved Visibility and Control
- With EDR, you gain deep insight into endpoint activity
- Zero-Trust extends that visibility to identity, application, and network access, giving you a better understanding of what is happening.
By integrating EDR and Zero-Trust, you can achieve a proactive, resilient security posture that mitigates risks in real time.
Conclusion
Traditional antivirus isn’t dead, but it is no longer enough. Think of it as just one layer of a much larger defense strategy. Threats aren’t slowing down, they are becoming more advanced, frequent, and damaging. By embracing modern security tools you can protect your company from today’s sophisticated attacks and tomorrow’s unknown threats. Please feel free to reach out to us if you have any questions.

